New research has unearthed multiple novel attacks that break Bluetooth Classic’s forward secrecy and future secrecy guarantees, resulting in adversary-in-the-middle (AitM) scenarios between two already connected peers.
The issues, collectively named BLUFFS, impact Bluetooth Core Specification 4.2 through 5.4. They are tracked under the identifier CVE-2023-24023 (CVSS score: 6.8) and were responsibly disclosed in October 2022.
The attacks “enable device impersonation and machine-in-the-middle across sessions by only compromising one session key,” EURECOM researcher Daniele Antonioli said in a study published late last month.
This is made possible by leveraging two new flaws in the Bluetooth standard’s session key derivation mechanism that allow the derivation of the same key across sessions.
While forward secrecy in key-agreement cryptographic protocols ensures that past communications are not revealed, even if the private keys to a particular exchange are revealed by a passive attacker, future secrecy (aka backward secrecy) guarantees the confidentiality of future messages should the past keys get corrupted.
In other words, forward secrecy protects past sessions against future compromises of keys.
The attack works by weaponizing four architectural vulnerabilities, including the aforementioned two flaws, in the specification of the Bluetooth session establishment process to derive a weak session key, and subsequently brute-force it to spoof arbitrary victims.
The AitM attacker impersonating the paired device could then negotiate a connection with the other end to establish a subsequent encryption procedure using legacy encryption.
In doing so, “an attacker in proximity may ensure that the same encryption key is used for every session while in proximity and force the lowest supported encryption key length,” the Bluetooth Special Interest Group (SIG) said.
“Any conforming BR/EDR implementation is expected to be vulnerable to this attack on session key establishment, however, the impact may be limited by refusing access to host resources from a downgraded session, or by ensuring sufficient key entropy to make session key reuse of limited utility to an attacker.”
Furthermore, an attacker can take advantage of the shortcomings to brute-force the encryption key in real-time, thereby enabling live injection attacks on traffic between vulnerable peers.
The success of the attack, however, presupposes that an attacking device is within the wireless range of two vulnerable Bluetooth devices initiating a pairing procedure and that the adversary can capture Bluetooth packets in plaintext and ciphertext, known as the victim’s Bluetooth address, and craft Bluetooth packets.
As mitigations, SIG recommends that Bluetooth implementations reject service-level connections on an encrypted baseband link with key strengths below 7 octets, have devices operate in “Secure Connections Only Mode” to ensure sufficient key strength, and pair is done via “Secure Connections” mode as opposed the legacy mode.
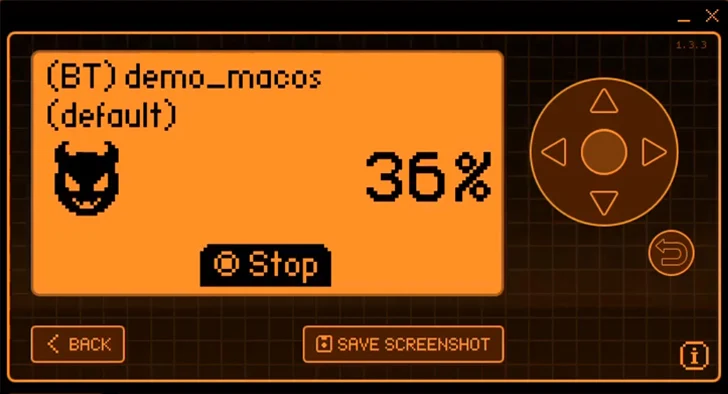
The disclosure comes as ThreatLocker detailed a Bluetooth impersonation attack that can abuse the pairing mechanism to gain wireless access to Apple macOS systems via the Bluetooth connection and launch a reverse shell.