 Hackers are using ZIP file concatenation to bypass security solutions and infect their targets with malware through email messages, experts have warned.
Hackers are using ZIP file concatenation to bypass security solutions and infect their targets with malware through email messages, experts have warned.
A new method in cyberattacks uses ZIP file concatenation to deliver malicious payloads undetected. By leveraging differences in ZIP parser handling, attackers can hide trojans in ZIP files, targeting unsuspecting users via phishing emails disguised as legitimate notices.
- ZIP Concatenation Technique: Hackers combine multiple ZIP files, each with separate content, into one archive to bypass detection mechanisms.
- Exploit of ZIP App Vulnerabilities: Different ZIP parsing tools, such as 7zip, WinRAR, and Windows File Explorer, interpret concatenated files differently, leading to varying visibility of hidden payloads.
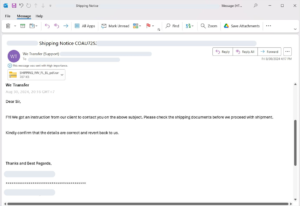
- Phishing Email Delivery: Attackers lure users into downloading the malicious archive through phishing emails, often disguised as notifications for shipping or other services.
- Payload Concealment: Using AutoIt scripting, attackers automate malicious tasks without detection by traditional anti-virus software.
- Defensive Measures: Security experts recommend recursive unpacking in security solutions and strict email filtering policies for ZIP and RAR files.
What You Should Do
Be aware of phishing emails, “warning” the victim of a pending invoice, or an undelivered parcel.
If you have questions or need assistance, contact a member of the BMT team.