Critical security flaws have been disclosed in the Open Authorization (OAuth) implementation of popular online services such as Grammarly, Vidio, and Bukalapak, building upon previous shortcomings uncovered in Booking[.]com and Expo.
The weaknesses, now addressed by the respective companies following responsible disclosure between February and April 2023, could have allowed malicious actors to obtain access tokens and potentially hijack user accounts.
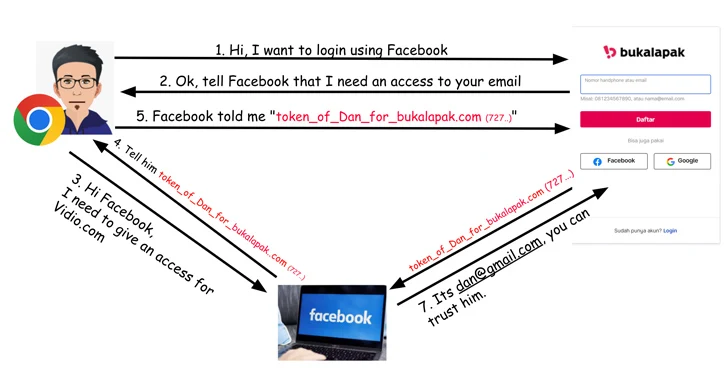
OAuth is a standard that’s commonly used as a mechanism for cross-application access, granting websites or applications access to their information on other websites, such as Facebook, but without giving them the passwords.
“When OAuth is used to provide service authentication, any security breach in it can lead to identity theft, financial fraud, and access to various personal information including credit card numbers, private messages, health records, and more, depending on the specific service being attacked,” Salt Security researcher Aviad Carmel said.
The problem identified in Vidio stems from an absence of token verification, meaning an attacker can use an access token generated for another App ID, a random identifier created by Facebook for every application or website that gets registered in its developer portal.
In a potential attack scenario, a threat actor could create a rogue website that offers a sign-in option through Facebook to collect the access tokens and subsequently use them against Vidio.com (which has the App ID 92356), thereby allowing full account takeover.
The API security firm said it also discovered a similar issue with token verification on Bukalapak.com via Facebook login that could result in unauthorized account access.
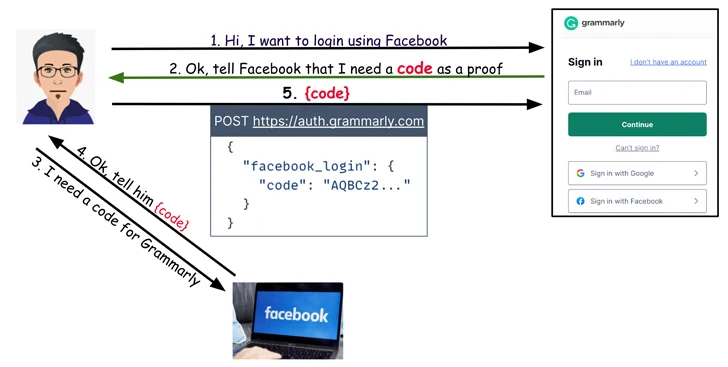
On Grammarly, it emerged that when users attempt to login to their accounts using the “Sign in with Facebook” option, an HTTP POST request is sent to auth.grammarly[.]com to authenticate them using a secret code.
As a result, while Grammarly is not susceptible to a token reuse attack like in the case of Vidio and Bukalapak, it is nonetheless vulnerable to a different kind of problem wherein the POST request can be altered to substitute the secret code with an access token obtained from the aforementioned malicious website to gain access to the account.
“And like with the other sites, the Grammarly implementation did not perform token verification,” Carmel said, adding, “an account takeover would give an attacker access to the victim’s stored documents.”